Play the game to
GET YOUR FREE APPLE AIRTAG!
“The Firm” has been hit with Ransomware! Follow the clues and correctly identify the culprit who provided the attack point via their unsecured endpoint and you win!
1) Review the clues below
2) Submit your guess
3) Guess correctly and get a FREE Apple AirTag
Meet the suspects

Game rules
We know you’re a maverick and you don’t play by the rules, but here they are anyway. You will test your cyber detective skills by reviewing the evidence and uncovering the 5 clues that will enable you to solve this puzzle. As a reward, the players who solve the cybersecurity conundrum will get A FREE Apple AirTag with case!
It is down to you to deduce the ‘who’, the ‘what’, and the ‘where’ that allowed the cyber-criminal to gain access to “The Firm”. Along the way, learn about IGEL’s smart, simple and secure Cloud VDI technology.
But remember – the clock is ticking. Be one of the top detectives to solve the case and win the prize!*
*While Supplies Last. Please see the Terms & Conditions for complete game rules.Find the clues
Test your cyber detective skills, review the evidence and uncover the 5 clues that will help you crack the case. Download our Detective's Notebook if you want to keep track of your investigation.
Mitigating Ransomware
Learn how one tiny device or simple software install can keep your organisation running in the event of a malicious cyberattack.


Securing your Edge
Advice on securing your edge in a riskier world, now that Working From Home has become a fact of life.
Secure your edge, the smart way
An introduction to today’s endpoint security risks – and a simple mitigation strategy.

Top 10 reasons to choose IGEL
We’ve put together the top 10 reasons to use IGEL as part of your endpoint security strategy.
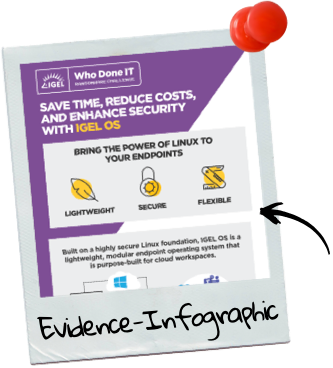
IGEL OS: Lower costs. Higher security.
All the reasons to add IGEL OS into your security strategy, in one simple infographic.
Spend less time worrying about endpoint security!
IGEL makes security simpler.
By converting any compatible x86-64 device into a fully functioning read-only cloud workspace, and moving Windows into the cloud, you immediately minimize endpoint attack surfaces, whether on licensed endpoints or on users’ own devices.
Submit your
final report
Have you followed the path? Found all the clues? Do you know “who done IT?”
Submit your final report, but be sure you’re right... you may only play the ransomware challenge once. No duplicate or redundant chances will be accepted.